6 Phases in an Incident Response Plan
An incident response plan should be set up to address a suspected data breach in a series of phases.

An incident response plan should be set up to address a suspected data breach in a series of phases.

An incident response plan is a documented, written plan with 6 distinct phases that helps IT professionals and staff recognize and deal with a cybersecurity incident like a data breach or cyber attack. Properly creating and managing an incident response plan involves regular updates and training.
Find out: Are you doing these 6 important things to prevent a data breach?
Yes, Requirement 12 of the PCI DSS specifies the steps businesses must take relating to their incident response plan, including:
See also: What are the 12 requirements of PCI DSS Compliance?
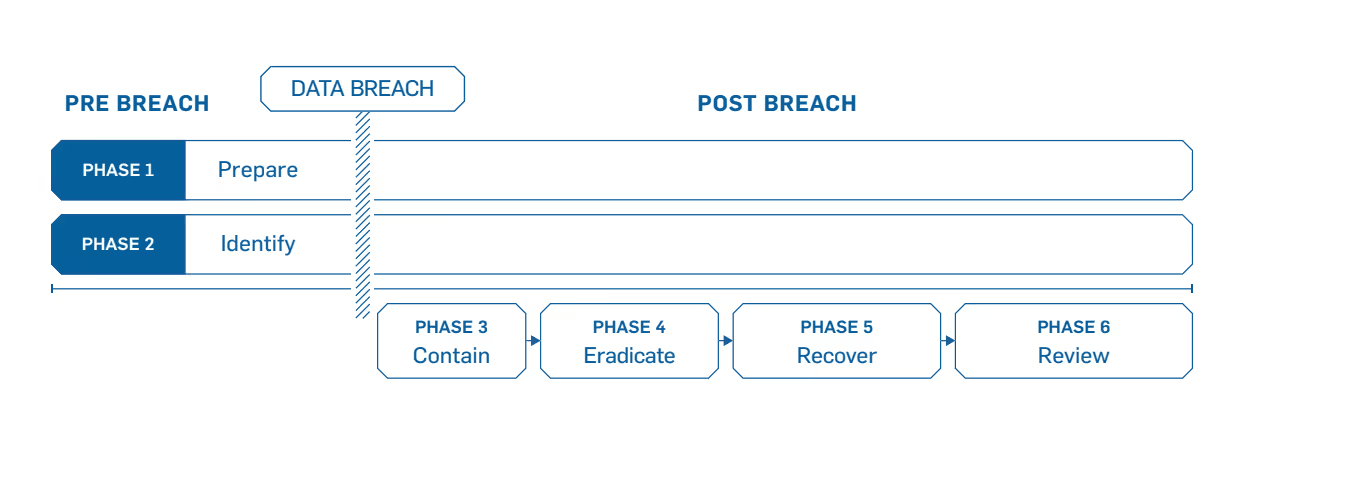
An incident response plan should be set up to address a suspected data breach in a series of phases. Within each phase, there are specific areas of need that should be considered.
The incident response phases are:
Let’s look at each phase in more depth and point out the items that you need to address.
See Also: 6 Steps to Making an Incident Response Plan
This phase will be the work horse of your incident response planning, and in the end, the most crucial phase to protect your business. Part of this phase includes:
Your response plan should be well documented, thoroughly explaining everyone’s roles and responsibilities. Then the plan must be tested in order to assure that your employees will perform as they were trained. The more prepared your employees are, the less likely they’ll make critical mistakes.
See also: 5 Things Your Incident Response Plan Needs
See also: Incident Response Plan White Paper
This is the process where you determine whether you’ve been breached. A breach, or incident, could originate from many different areas.
When a breach is first discovered, your initial instinct may be to securely delete everything so you can just get rid of it. However, that will likely hurt you in the long run since you’ll be destroying valuable evidence that you need to determine where the breach started and devise a plan to prevent it from happening again.
Instead, contain the breach so it doesn’t spread and cause further damage to your business. If you can, disconnect affected devices from the Internet. Have short-term and long-term containment strategies ready. It’s also good to have a redundant system back-up to help restore business operations. That way, any compromised data isn’t lost forever.
This is also a good time to update and patch your systems, review your remote access protocols (requiring mandatory multi-factor authentication), change all user and administrative access credentials and harden all passwords.
See Also: SecurityMetrics Learning Center
Once you’ve contained the issue, you need to find and eliminate the root cause of the breach. This means all malware should be securely removed, systems should again be hardened and patched, and updates should be applied.
Whether you do this yourself, or hire a third party to do it, you need to be thorough. If any trace of malware or security issues remain in your systems, you may still be losing valuable data, and your liability could increase.
This is the process of restoring and returning affected systems and devices back into your business environment. During this time, it’s important to get your systems and business operations up and running again without the fear of another breach.
Once the investigation is complete, hold an after-action meeting with all Incident Response Team members and discuss what you’ve learned from the data breach. This is where you will analyze and document everything about the breach. Determine what worked well in your response plan, and where there were some holes. Lessons learned from both mock and real events will help strengthen your systems against the future attacks.
No one wants to go through a data breach, but it’s essential to plan for one. Prepare for it, know what to do when it happens, and learn all that you can afterwards.
Need help with a data breach? Talk to one of our Forensic Investigators.